Smart contract audits. Penetration testing. Bug bounties. Infrastructure hardening.
These are the security investments crypto companies make — and they’re essential.
But there’s another surface area that shapes user protection outcomes: support operations. In the context of crypto BPO security, this means every interaction where agents access user data, verify identities, or handle sensitive account information.
The Industry Has Noticed
Support operations are becoming a strategic consideration in security planning — not as a risk, but as an opportunity to build trust by design.
The data supports this shift. Venminder’s State of Third-Party Risk Management 2025 report shows 30% of data breaches stem from security alignment gaps between organizations and their operational partners — a 15% increase from 2023. For companies evaluating secure crypto support partnerships, this highlights why working with teams founded on security DNA and compliance standards matters.
In crypto, where blockchain customer service teams handle sensitive user data daily, these numbers carry particular weight.
The Numbers Tell the Story
In 2024, Americans filed over 149,000 crypto-related complaints with the FBI. Losses totaled $9.3 billion — a 66% increase from the previous year.
The CFPB’s complaint bulletin noted a pattern: poor customer service is a common theme across crypto-related complaints.
These represent users who reached out for help and encountered operations that weren’t equipped to protect them.
Insider Incidents: What the Data Shows
The crypto support insider threat conversation is backed by hard numbers. According to the Ponemon Institute’s 2025 Global Report, insider-related incidents now cost organizations an average of $17.4 million annually — up from $16.2 million in 2023.
Key findings: organizations experience an average of 13.5 insider incidents per year. Each incident costs approximately $676,517 to resolve. It takes an average of 81 days to contain an insider-related incident.
Verizon’s 2025 Data Breach Investigations Report adds context: 89% of malicious insider breaches are financially motivated.
In crypto, where transactions are irreversible, these numbers matter.
An Evolving Landscape
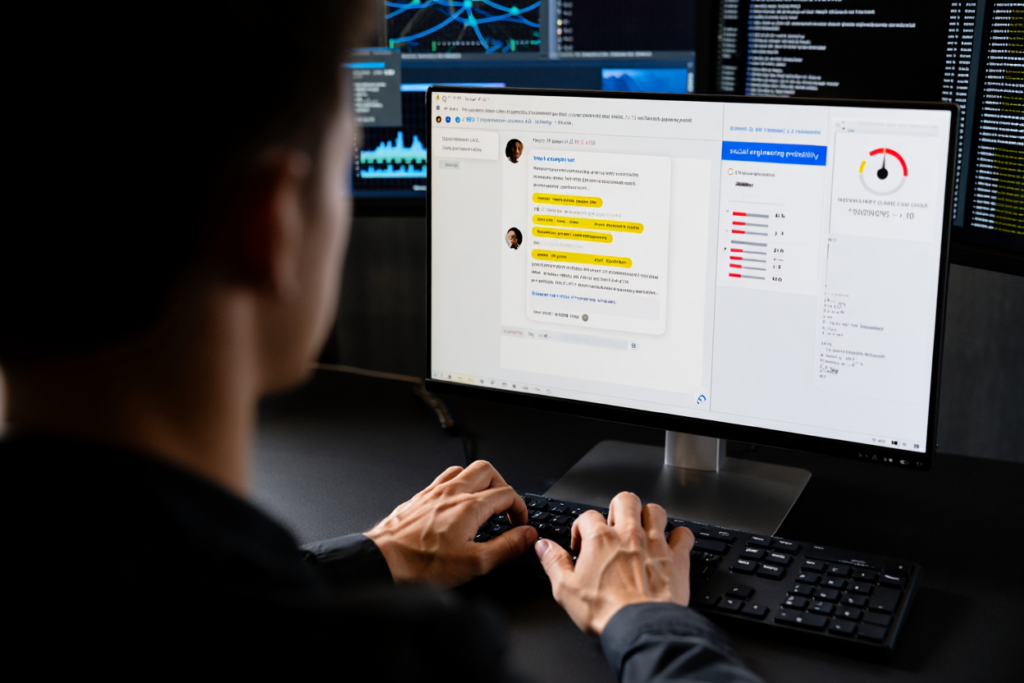
Palo Alto’s Unit 42 Global Incident Response Report documented a shift in 2024–2025: more than one-third of social engineering incidents involved help desk manipulation.
CrowdStrike’s 2025 Global Threat Report adds that voice phishing attacks increased 442% between the first and second halves of 2024.
The role of support operations in overall security strategy is getting more attention — from companies and regulators alike.
What Security DNA Looks Like
What separates support operations that consistently protect users?
Security DNA is organizational. It’s embedded in how a company is built — not just who works there. For compliant crypto operations, this means five structural dimensions working together:
Governance and compliance frameworks. Formal policies, certifications like PCI-DSS and SOC 2, and alignment with regulatory standards that create accountability at every level.
Security architecture. Access controls, encrypted infrastructure, activity monitoring, and facility protocols that protect sensitive data by design.
Operational design. Workflows built with segregation of duties, clear escalation paths, and processes that minimize exposure at every touchpoint.
Organizational culture. Leadership that visibly prioritizes user protection, continuous training, and accountability structures that reinforce security as daily practice.
Continuous improvement. Regular audits, threat monitoring, and the ability to evolve controls as the landscape changes.
These are the structural factors that shape how a secure crypto support operation performs.
Regulators Have Noticed
In May 2024, NYDFS issued new guidance requiring crypto service providers to implement formal complaint resolution mechanisms with quarterly analysis.
Support infrastructure is now compliance surface area.
This signals regulatory recognition that how companies support their users — through blockchain customer service operations — connects directly to user protection outcomes.
The Opportunity
When evaluating support operations, resolution times and cost per interaction are part of the picture. The broader question is how the operation is built — the organizational DNA that shapes daily decisions and long-term outcomes.
In crypto, where user trust is foundational, support operations that embody security as a core value create a meaningful advantage.
We’ve got your back. Crypto-native.
Ready to explore what this looks like? Let’s talk.